Delivering a satisfying online customer experience is critical for any organization with a web presence. A big part of this is trust is fulfilled by Identity verification. Most customers will shy away from a website or app that does not appear trustworthy.
Here is why every organization should be taking the right steps to protect its user’s personal information during online transactions. Getting a customer to trust you today means they will do business with you tomorrow.
Identity Proving has been a challenge for about 20 years. protecting online accounts of customers & meeting regulatory and compliance guidelines are concerns that highlight the importance of this issue.
Service providers & organizations always are looking for optimal protection methods while maintaining user frictionless online access and improving the user experience.
In this article, we’ve provided a summary of 3 popular online verification methods, each with its pros and cons.
Knowledge-Based Authentication (KBA)
Knowledge-based authentication (KBA) is a security measure that verifies a person’s identity by requiring an answer to at least one security question like:
- What’s your mother’s maiden name?
- What was your first teacher called?
- What was your first pet?
- ….

These questions while seemingly simple and answered quickly by anyone, are difficult for those who intend to misuse information.
Another method of information care that is considered in KBA is to limit the response time. If the real customer wants to access the information, they can answer these questions quickly.
This method is very optimal for the user in terms of simplicity. But with the growth of social networks and access to information of people on social media and other networks, it is possible to get answers to these questions. This is perhaps one of the biggest drawbacks of the KBA method.
KBA questions can be static or dynamic. Static KBA has no way of dealing with information purchased by Internet fraudsters. This is why the static KBA method is becoming less and less popular. Access to information such as high school, pet name, spouse name, etc. through the social networks of people is very easy, and make static KBA will be less reliable. Advanced Dynamic KBA customizes customer questions using proprietary data stored behind a firewall, and will be a great authentication solution for online authentication.
Two-Factor Authentication (2FA)
Two-factor authentication (2FA) is a special type of multi-factor authentication (MFA) that examines customer access through two methods of authentication and security. These two methods are also called authentication agents.

In general, 2fa means that the user confirms his identity in two different and separate steps.
There are different factors for authentication by the …. method, some of which I will examine below.
Knowledge: This includes information that the actual user is aware of, such as a password or security question
Possession: This factor relates to items owned by the user. Like a cell phone that can receive a code.
Biometric data: This is related to the user’s biological characteristics that can be used for authentication, such as fingerprints, retina scans, and face identifiers.
Location: GPS can be used to authenticate the user by restricting to a specific geographical area.
It is not necessary to use two different factors for the method 2FA For example, both steps of authentication may be done by entering a password.
These days, the possibility of internet theft using users’ passwords has become easier for attackers, so the 2FA method is becoming more and more popular.
With the onset of the corona pandemic and the increase in telecommuting, the importance of authentication has also become more prominent. You can use the 2FA method to secure their connections and authenticate them.
Security experts always use the method 2FA if possible. However, there are some disadvantages to the 2FA method.
۲FA may annoy older or less knowledgeable users and they may not have easy access to their applications.
Also, not all users of modern smartphones need the many 2FA methods, or mobile Internet access is very expensive in some countries and has economic consequences.
Setting up 2FA may also cost small businesses money and they may ignore it.
Biometric Authentication
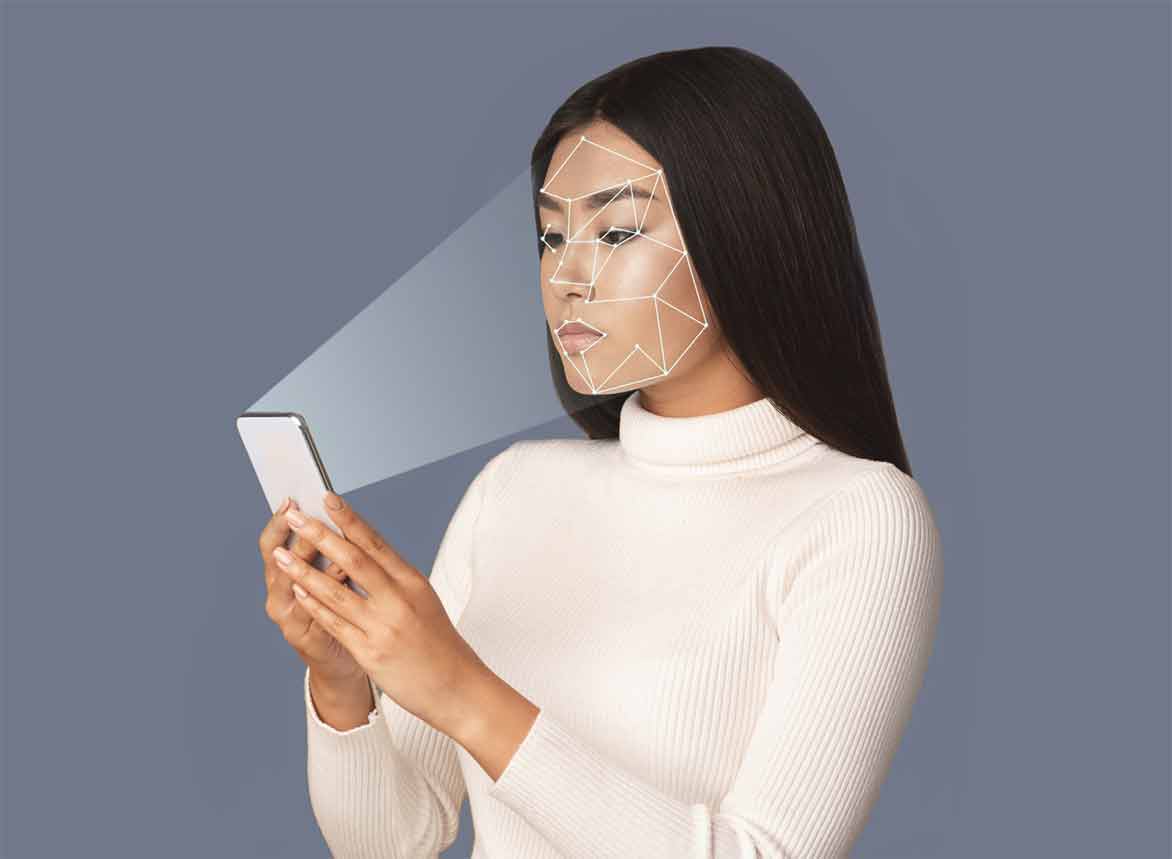
Biometric authentication is a type of authentication that is measured by a person’s biological characteristics, such as fingerprints, ear-and-ear edge geometry, retinal patterns, cheddar, and written signatures.
The oldest form of biometric authentication is the use of the fingerprint method. This method is probably the most common. Because millions of people use it daily through their mobile phones. This method relies on the unique characteristics of people compared to others.
But the question is, what about other biometric methods?
Another way is voice recognition to identify and authenticate customers.
Another common form of biometrics is face recognition technology. Any device with a camera can support this type of technology. This feature is also active on many mobile phones.
Biometrics are more secure than other methods of authentication. Because it relies on unique features that are not easily stolen and generally use artificial intelligence algorithms for comparison and the process is very accurate.
Passwords are also less secure and it is very common for customers to forget them.
Security questions are also a bit difficult for users, despite better security.
Finally, the biometric method, based on individual characteristics such as the face, is easy and unforgettable, and it is very difficult to steal.
Of course, this method also has disadvantages. For example, imagine using this method to open a bank account. In this case, you must visit the bank in person and enter your biological information.
Conclusion:
We have summarized the three most popular Identification methods & their pros & cons. To conclude the issue, the most accurate way to verify someone’s identity is to request and validate more than one form of identification against the person standing in front of you, with at least one of them being a photo ID. But we should never forget to make the balance between user’s comfort & frictionless activity and security safeguarding.
References:









